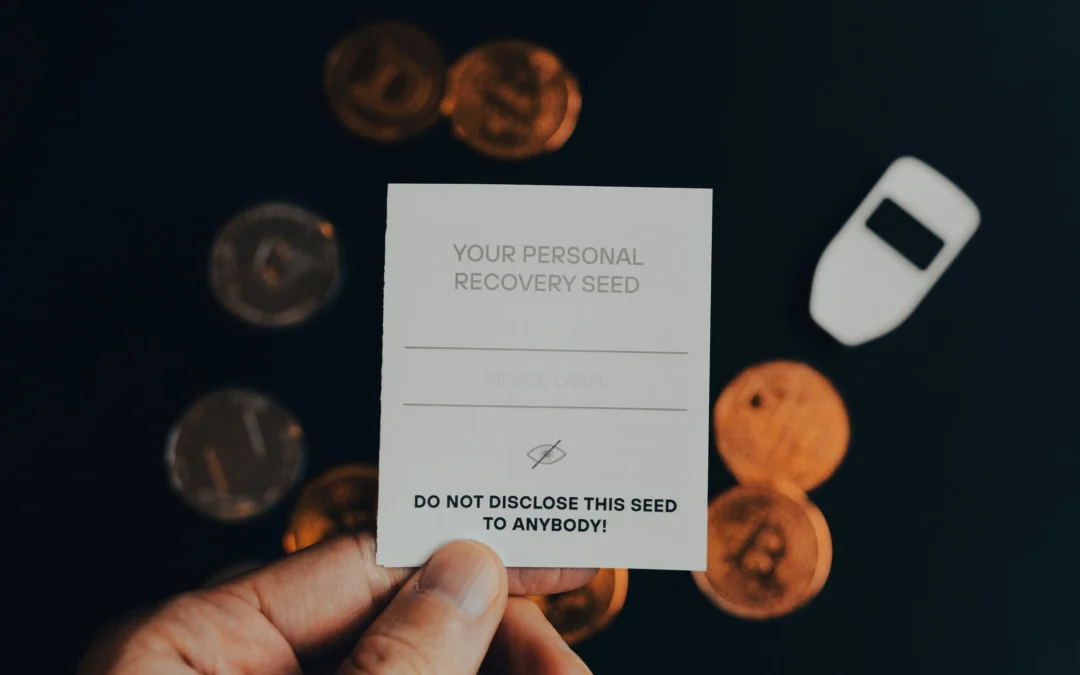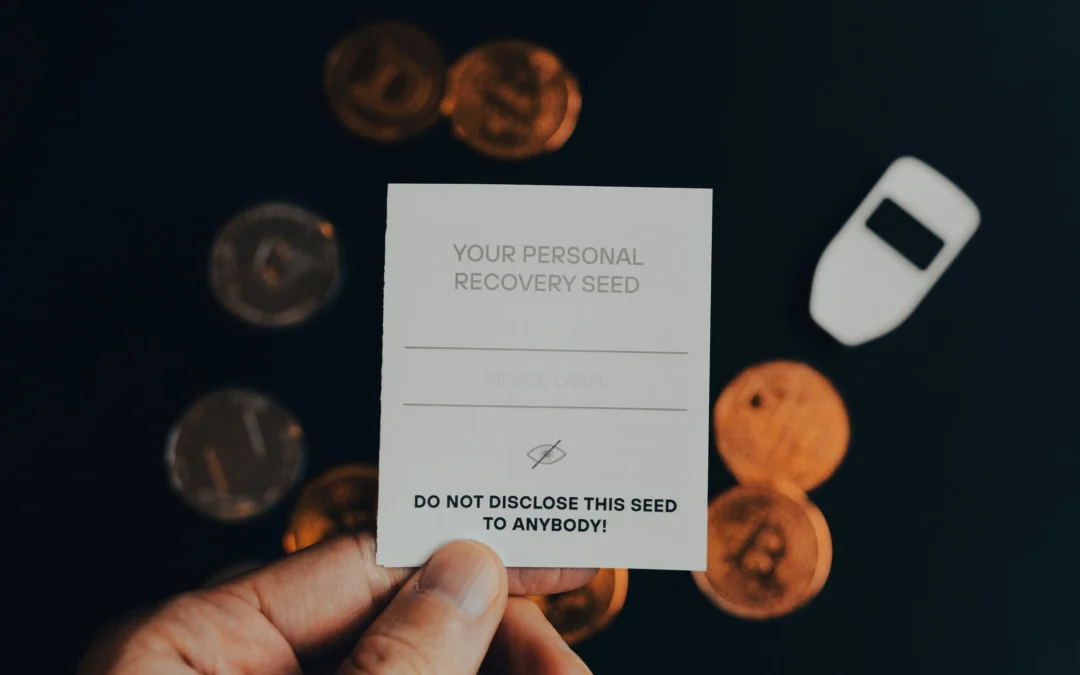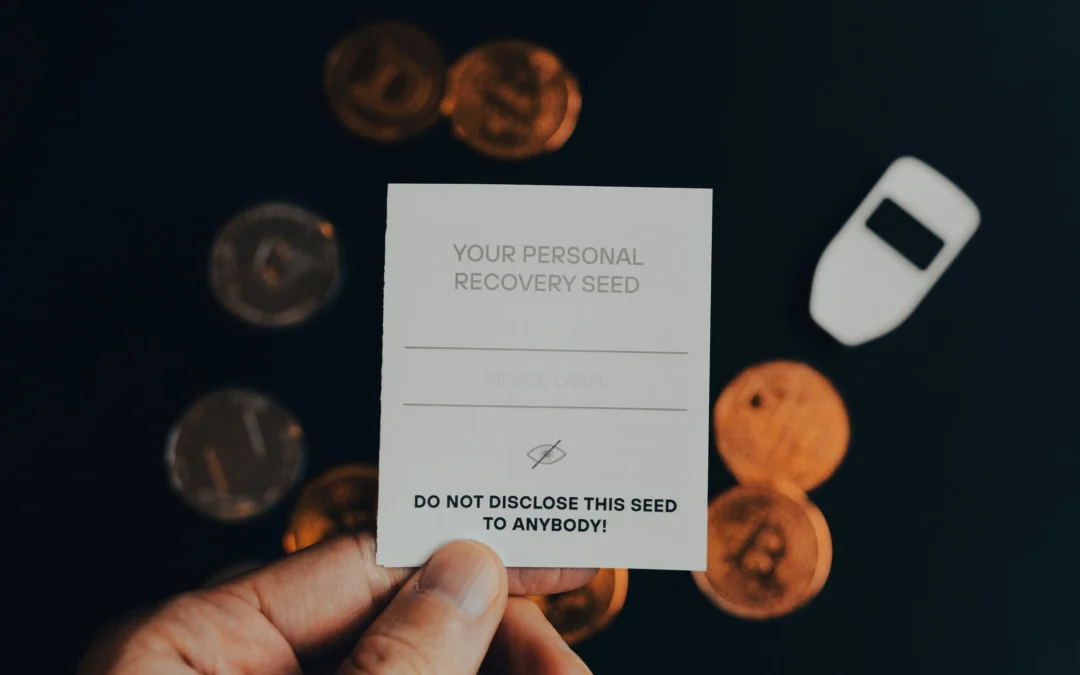
by Hunt Sanja | Sep 19, 2025 | Crypto
Losing control of your seed phrase security can put your entire crypto portfolio at serious risk. According to Chainalysis, more than $2.17 billion in cryptocurrency was stolen during the first half of 2025. In many cases, the problem started with something simple:...

by Hunt Sanja | Aug 14, 2025 | Hackers
Security holes can exist from the moment your system is deployed, even before it reaches users. According to Comparitech, 84% of companies face critical weaknesses on their network perimeters, which can be exploited by threat actors such as wifi hackers. This...

by Hunt Sanja | Jul 24, 2025 | Tutorials
Every time we agree to the terms of use without reading them, we leave personal data stored on sites we’ve long forgotten: names, email, location, or even photos being shared in public spaces that you can no longer control. A Surfshark report revealed that over 300...

by Hunt Sanja | Jun 27, 2025 | Hackers
When celebrities get hacked, the entire internet feels the impact. Private photos leaked, personal conversations exposed, social media accounts hijacked and used to send fake news or scams. We’ve all seen the headlines, glamorous names turned into warning tales....

by Hunt Sanja | Jun 17, 2025 | Hackers
Social media brings a lot of benefits, but it’s also a common entry point for cyberattacks. According to the New York Post, by October 2024, 45% of people had experienced a cyberattack—nearly half of them through their social media accounts. In this post, we’ll...